Most B2B cybersecurity companies describe themselves the same way. Advanced threat detection. AI-powered protection. Zero trust architecture. The language is technically accurate and almost completely interchangeable.
That’s the actual problem. Cybersecurity is different from almost every other B2B category because buyers can’t evaluate your product’s quality before they need it. They’re making high-stakes, multi-year decisions almost entirely on trust signals. If your brand looks and sounds like every other vendor in their evaluation stack, the differentiation battle is already lost before anyone reads a datasheet.
According to Edelman research, 81% of consumers need to trust a brand before buying, and 70% will pay more for brands they trust. In the B2B cybersecurity space, where contracts reach millions and a single breach can end careers, that trust multiplier is even higher.
Building a strong cybersecurity brand isn’t about showcasing your technology features. It’s about making decision-makers confident in your expertise long before they’re in a position to evaluate your product. Whether you’re a cybersecurity startup building credibility from scratch or an established player whose brand has drifted out of step with the market, this guide covers the strategies, examples, and trends shaping what works in 2026.
Proven Cybersecurity Branding Strategies That Build Trust
Effective cybersecurity branding means more than a polished logo and tagline. In a market where buyers are skeptical by default and vague claims are actively ignored, it means building the kind of credibility that gets you onto the shortlist before the evaluation even begins.
Define a position that actually means something
Most cybersecurity vendors compete on the same three variables: speed, intelligence, and protection. That’s not differentiation. Those are table stakes.
The question isn’t what your company does. It’s what makes your company the right fit for a specific type of buyer in a specific situation. Are you the platform built for organizations navigating healthcare compliance? The team with years inside the OT environments you’re protecting? The vendor that can translate a breach investigation into clear language for the board, not just the CISO?
Positioning that means something requires being specific enough to exclude some buyers. That’s uncomfortable, but it’s the only way to be credible to the right ones. We’ve done this positioning work with cybersecurity clients including Kount, Splunk, Sift, and Digimarc — companies operating in some of the most competitive corners of the security market, where generic claims are immediately disqualifying.
Build thought leadership that demonstrates judgment
In cybersecurity, thought leadership earns trust when it demonstrates judgment, not just knowledge. Publishing a “what is zero trust” explainer in 2026 signals you’re behind the conversation. Publishing a rigorous analysis of where zero trust implementations fail in practice, with specific evidence, establishes authority.
What actually works:
- Original research and threat intelligence reports that reveal something buyers don’t already know
- Conference presentations with a defined point of view, not product walkthroughs
- Expert commentary in outlets like Dark Reading or SC Media when significant incidents happen
- Technical depth that only a company with real field experience could produce
CrowdStrike’s Global Threat Report is the standard. It became an industry reference document because it was genuinely useful intelligence to security practitioners — including people who weren’t CrowdStrike customers. The brand benefited from the content’s credibility, not the other way around.
Build a website that earns credibility over time
Cybersecurity sales cycles are long. Buyers research for months before making contact. Your website isn’t just a first impression, it’s the place buyers return to repeatedly as they build conviction (or lose it).
Generic whitepapers and recycled blog posts signal that your company produces content for SEO, not for security practitioners. Sophisticated buyers notice. What earns sustained credibility:
- Case studies with specific metrics and named client challenges
- Technical guides that demonstrate genuine expertise, not just topic coverage
- FAQ content that addresses what buyers actually search for at each stage
- Resources organized around the buyer’s problem, not your product features
This approach positions your brand as a reliable resource while encouraging repeat engagement throughout the buyer’s journey.
Tailor messaging to the buying committee
A cybersecurity purchase rarely comes down to one decision-maker. CISOs, IT managers, compliance officers, CFOs, and sometimes the board all have a stake. The mistake most cybersecurity brands make is writing for one audience and leaving the rest to figure out why they should care.
Tailor messaging by role:
- CISOs and security leads: operational credibility, track record, integration with existing infrastructure
- CFOs and executives: risk reduction framing, total cost of ownership, regulatory exposure
- Compliance officers: framework alignment (NIST, ISO 27001, SOC 2), audit readiness, documentation
- IT managers: implementation complexity, support quality, technical depth
The same product, positioned correctly for each audience, performs very differently in a buying process.
Visual identity: what cybersecurity buyers are actually reading
The visual language of cybersecurity has shifted. Dark backgrounds, padlock icons, and circuit board imagery have given way to cleaner, more human-centered design. Heavy “cyber aesthetic” branding now reads as a signal of a product company, not a trusted partner.
Strong cybersecurity brand visuals communicate three things: clarity (the company can explain complex things simply), professionalism (you’d trust this organization with your most sensitive systems), and distinctiveness (this doesn’t look like the other vendors in the evaluation stack). Consistency across touchpoints matters more in cybersecurity than most categories because buyers encounter your brand over many months before making contact.
Cybersecurity Branding Examples: What Leading Companies Do Right
Theory only goes so far. Let’s look at how leading cybersecurity companies put these branding strategies into action, and what B2B marketers can learn from their approaches.
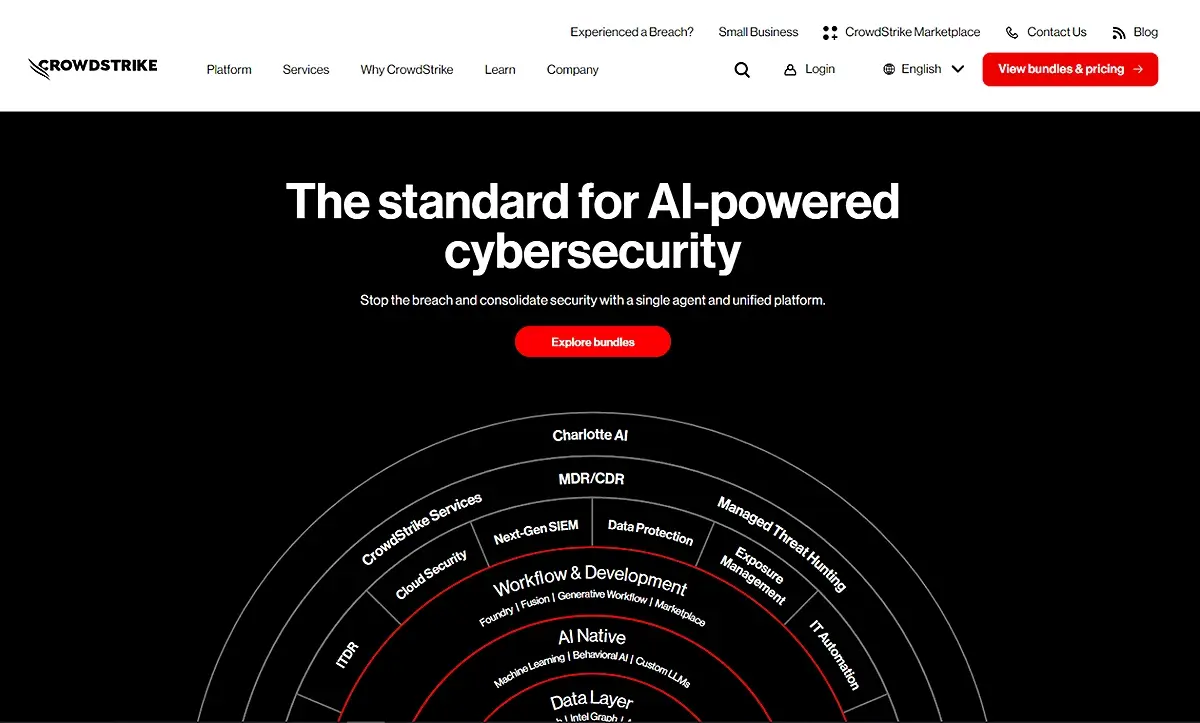
Content-driven authority: CrowdStrike
CrowdStrike’s brand strength didn’t come from their logo or their tagline. It came from producing intelligence that the security industry actually needed. The Global Threat Report became a reference document that practitioners cite regardless of whether they’re CrowdStrike customers. The brand benefited from the content’s credibility.
The lesson: if your content is genuinely useful to a security practitioner outside a sales context, it builds the kind of trust that paid media can’t replicate. Free risk assessments and tools that provide immediate value generate qualified leads while demonstrating your capabilities in practice.
Putting the human factor forward: Kaspersky
Kaspersky’s shift toward user education and behavior-based security reflected something most enterprise cybersecurity vendors still underweight: people are simultaneously the weakest link and the first line of defense in any security strategy. Their content reflected that understanding with practical, human-focused guidance rather than technical specifications.
The B2B takeaway: a security solution that talks about how it works for people — not just for infrastructure — reaches decision-makers who’ve watched technically capable solutions fail to prevent human-driven threats.
5 Key Cybersecurity Branding Trends Shaping 2026
1. Returning to a More Human-Centric Approach
The emphasis on technology as a cybersecurity differentiator produced a wave of cold, technical digital experiences. That’s changing. Cybersecurity companies are increasingly focusing on what their solutions do for people: user education, behavior-based security approaches, and communications that treat employees as active participants in security rather than liabilities to be managed. This is important because people are both the weakest link in any enterprise cybersecurity strategy and the first line of defense.
By pulling back from talking about tools and technology to instead consider the customers and employees who are using them, cybersecurity content and writing naturally feel more human. Kaspersky’s “human factor” positioning set an early example that much of the industry has been catching up to.

2. Increased Emphasis on Digital Brand User Experience (UX)
With the B2B cybersecurity space becoming more and more crowded, brands are realizing it’s no longer enough to simply showcase their products. To stand out from the competition, you have to craft a superior digital brand experience. That means putting more thought into who your target personas are and what they want to accomplish and creating specific user journeys and flows to help them get there quickly and easily—from decision-makers and influencers to everyday users.
This is also part of the broader shift away from a more product- and solution-centric view, with the emphasis instead being on the people using your solutions. Commvault does an excellent job of combining clear messaging with intentional user journeys to create a standout digital brand experience.
3. AI and Machine Learning Integration
In 2026, if AI and machine learning (ML) aren’t part of your cybersecurity solution, you’re behind the market — and probably out of the game. Not only will your technology seem outdated, it won’t move at the speed and scale needed in today’s cybersecurity landscape.
According to IBM’s 2026 X-Force Threat Intelligence Index, vulnerability exploitation is now the leading cause of cyberattacks — with a 44% spike in attacks targeting public-facing applications last year. Organizations that fully deploy AI and automation programs contain breaches 28 days faster than those without. That’s a specific, credible claim. The brands winning with AI positioning aren’t just saying they have AI — they’re explaining what their implementation does that competitors’ doesn’t, and backing it with evidence buyers can evaluate.
But it’s not just about having these technologies. It’s about using them in a way that makes your products truly stand out and making that a meaningful part of your brand messaging. Crowdstrike does a good job of infusing AI and ML into both the product and brand story rather than just giving it lip service.
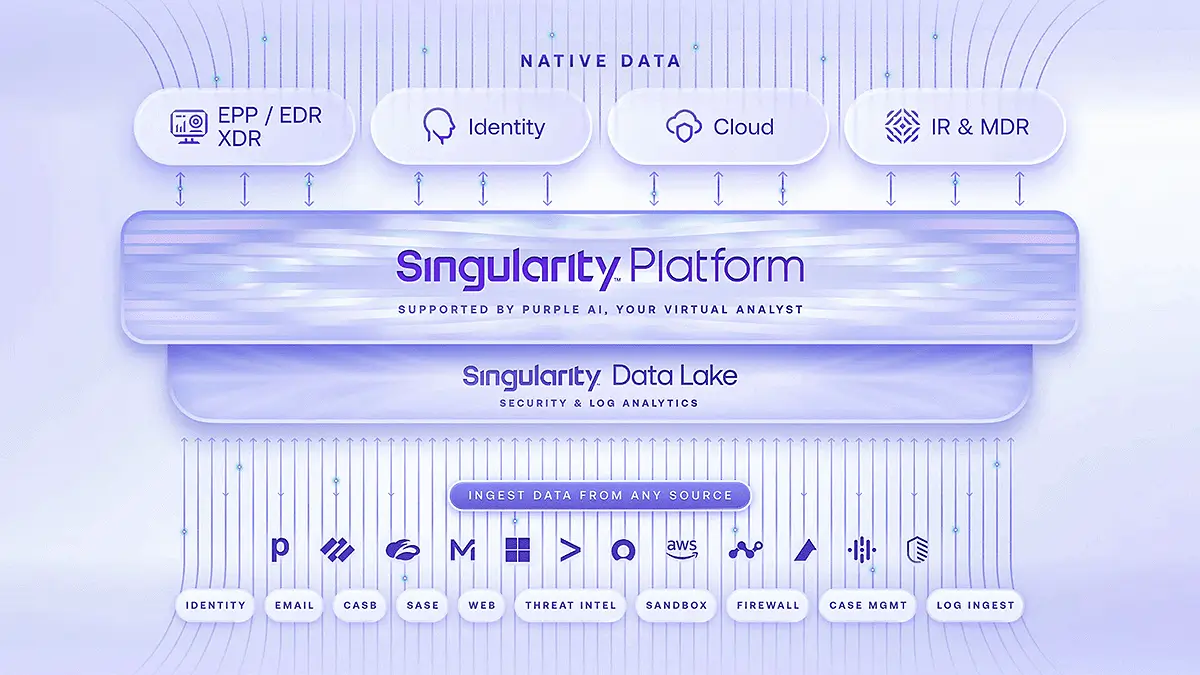
4. Integrated Security Platform Diagrams
To stay ahead of fast-moving and changing cyber threats, businesses are moving away from traditional standalone security products in favor of integrated security platforms that offer comprehensive protection across multiple attack vectors. It’s a natural progression for cybersecurity companies. From a B2B brand perspective, we see this brought forward with infographics and diagrams that often spotlight features such as threat intelligence, network security, endpoint security, and identity and access management (IAM). The diagram on SentinelOne’s site is a good example.
Moving away from product-based messaging also impacts site navigation, with the shift to platform-based messaging driving content, impacting how you message and how you go to market. We’re seeing many B2B clients use similar visuals to deepen engagement on their websites from both a brand and experience perspective.
5. Cybersecurity Awareness Campaigns
There’s been a recent resurgence in cybersecurity brands engaging in public awareness campaigns aimed at educating users about emerging threats, best practices for cybersecurity hygiene, and the importance of proactive security measures. This may be partly due to the return of the big trade shows following a pandemic-driven lull. From a B2B brand standpoint, it’s all about creating more content and increasing your digital presence. We’re talking banner ads, social media campaigns, blog posts (like this one from Microsoft), and so on. Anywhere you can get your message out there creates buzz around your brand and helps to drive engagement.
The brands that execute this well keep the focus on the people they’re helping rather than the products they’re selling. If there’s a consistent theme across effective cybersecurity marketing right now, it’s that people-centered storytelling consistently outperforms feature-centered storytelling. Awareness campaigns are one of the highest-visibility places to demonstrate that orientation.
Navigating Cybersecurity Branding Challenges
Building a strong cybersecurity brand isn’t without obstacles. Here are the common challenges our cybersecurity clients face, and how to address them.
Challenge 1: Standing out in a crowded, competitive market
The cybersecurity market is saturated with solutions making similar claims. Differentiation requires more than listing features, it demands clear positioning, compelling storytelling, and consistent proof of value.
Define a specific niche or differentiated positioning. Instead of being “another endpoint security solution,” become “the only solution built specifically for healthcare organizations with legacy infrastructure”. Then prove it with targeted case studies and persona-specific messaging.
Challenge 2: Bridging technical and executive audiences
CISOs speak in threat vectors. CFOs speak in risk exposure and total cost. Most cybersecurity brands write for one audience and lose the other.
A two-tier content strategy is the practical answer: technical depth for practitioners (threat analysis, integration guides, implementation documentation) alongside business-outcome framing for executives (what a breach costs in your specific industry, how this solution reduces regulatory exposure, what the ROI case looks like). These aren’t separate brands. They’re the same brand speaking two languages for two different stages of the same buying process.
Challenge 3: Keeping pace with a rapidly evolving threat landscape
A cybersecurity brand that looks slow to respond to a major incident or emerging threat loses credibility faster than brands in almost any other category. Buyers expect vendors to have an informed perspective when the landscape shifts.
Building an agile content operation — the ability to publish a substantive response to a new attack vector or regulatory change within days — is a real competitive differentiator. It demonstrates the operational readiness that buyers are implicitly evaluating when they read your content and decide whether you’re the kind of partner they can rely on when it matters.
Frequently Asked Questions
What makes cybersecurity branding different from other B2B marketing?
Cybersecurity buyers face a specific challenge: they can’t evaluate a product’s quality until they need it, and by then it’s too late for evaluation. That puts unusual weight on trust signals — brand credibility, thought leadership, demonstrated expertise, and peer references — long before any technology evaluation begins. In most B2B categories, a strong product demo can move a sale forward. In cybersecurity, the brand has to do more of that work before the demo happens.
How do cybersecurity companies build trust with enterprise buyers before the first meeting?
Consistently producing content that demonstrates genuine expertise is the most reliable path: threat intelligence, technical analysis, and depth that only a company with real field experience could produce. Named case studies with specific outcomes matter more in cybersecurity than in most categories because buyers rely heavily on third-party validation. Clear positioning, professional visual identity, and a website that answers buyers’ real questions rather than pitching at them all contribute to the trust that earns you a spot on the shortlist.
What should a B2B cybersecurity company’s website prioritize?
Clarity, credibility, and usefulness. Most cybersecurity websites prioritize feature lists and generic trust claims. What buyers actually need: a clear explanation of what makes this company different and for whom, proof in the form of named case studies and measurable outcomes, resources that are genuinely useful to a security practitioner (not just SEO content), and a path to a relevant next step that doesn’t force premature commitment. The companies that convert best make it easy for the right buyer to self-qualify quickly.
Where to Start
Most cybersecurity brand improvements don’t require a full rebrand. The highest-impact changes are usually more targeted: positioning specific enough to mean something, content that demonstrates genuine expertise rather than just covering topics, and a digital experience that helps the right buyers move forward quickly.
Clear Digital has worked with cybersecurity companies at every stage — from early-stage startups building credibility from scratch to enterprise players whose brand has drifted behind the market. Our work with clients including Kount, Splunk, Sift, and Digimarc covers brand positioning, digital experience design, and content strategies built for the long sales cycles and skeptical buyers that define this market.